 If fire breaks out in a building, you wouldn’t run out and buy and extinguisher to fight it after the fact. You’d likely already have one. The same idea should apply to cyber insurance, and yet insurers aren’t looking at how to reduce risks before breaches hit, an industry expert at RIMS 2017 asserted.
If fire breaks out in a building, you wouldn’t run out and buy and extinguisher to fight it after the fact. You’d likely already have one. The same idea should apply to cyber insurance, and yet insurers aren’t looking at how to reduce risks before breaches hit, an industry expert at RIMS 2017 asserted.
“We have to step back and not just look at cyber from an insurance perspective,” said Martin Frappolli, senior director of Knowledge Resources at The Institutes said during a session at the Risk Management Society’s 2017 conference in Philadelphia on April 25. “Cyber presents a set of risks organizations need to plan for … most cyber breaches are [from] a failure to prepare and plan.”
Frappolli noted that fire used to be considered “too dangerous, too unpredictable to be an insurable risk.” But over time, building owners and risk managers and insurers developed “good hygiene” designed to manage the risk of fire beyond simply having an insurance policy.
“Fire is still a very real risk but it is a well-managed one,” Frappolli said. “We all do fundamental things [to minimize risk] and then we buy insurance, just in case.”
That reality is something to keep in mind with the risk of cyber breach, which is fast-evolving and still relatively new in the marketplace, he added.
“Cyber … is new and scary,” and companies struggle to find the best way to insurer against it, Frappolli said. But companies can reduce their anxiety about cyber by approaching it the way they do the risk of fire. He said using risk control methods first, either through risk management expertise in-house, or “experts on speed dial” will help make cyber more manageable, and then the policy should be written based on those steps taken to make cyber breaches less likely.
One Way to Manage Cyber Risk: Modify Employee Behavior
Frappolli gave an example of where a simple risk management move – managing employee behavior – could make a difference in terms of managing cyber breach risks. He told a story about hackers who wanted to hack data. They’d visit large organizations’ unsecured areas and use the restroom, leaving behind USB sticks in the restroom labeled “confidential salary information.” Employees ended up taking the USB sticks and plugging them in to figure out what their colleagues were getting paid. But the USB sticks were rigged to retrieve data.
Scott Stransky, of AIR Worldwide/Verisk Analytics, who also spoke during the session, said the cyber underwriting process by gathering as much disparate information as possible The idea behind this: there could be connections that underwriters may not necessarily have considered before.
“At the time of underwriting, really understand the risk you are writing,” Stransky said.
This means collecting types of data such as the type of server a company uses, what is it’s DNS hosting service (which runs domain name system servers), and whether it uses vendors such as Paypal, among other points of information.
“At the end, it makes the world more resilient,” Stransky said. “It will help the insurance industry pay claims better, [and] understand the virtual supply chain for insuring against cyber risks.”
Stransky said underwriters can and should run scenarios based on this information, and that “some output from these scenarios can give insights as to how seemingly independent parts of the book of business are related.”
For now, though, cyber risk is untamed territory, and Frappolli urged insurers and risk managers to “pay attention as it evolves,” because “as it evolves, our approach to managing it is going to evolve.”
“It really is quite scary,” Frappolli added. “We buy fire insurance at the same time we buy a fire extinguisher. We know what to do with fire, but are still figuring out with cyber.”





















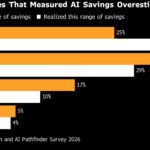 AI Savings Misses ‘Should Be Making Executives Uncomfortable,’ Bain Says
AI Savings Misses ‘Should Be Making Executives Uncomfortable,’ Bain Says  Multiple Factors Affect Auto, Workers Comp Claim Complexity: Report
Multiple Factors Affect Auto, Workers Comp Claim Complexity: Report  Suspects Indicted for Impersonating Shipping Carriers in $5M Multi-State Theft Ring
Suspects Indicted for Impersonating Shipping Carriers in $5M Multi-State Theft Ring  A $10.5 Trillion Cyber Problem: Whose Risk Is It Anyway?
A $10.5 Trillion Cyber Problem: Whose Risk Is It Anyway? 







